The Digital Adversary - Our Stealth Entertainment Project
The Hunter Becomes The Hunted
The rapid adoption of computing in mobile devices, financial transactions, communications and industrial controls has given rise to modern threats from eCriminals and adversarial nations attempting to seize gains in wealth and political control.
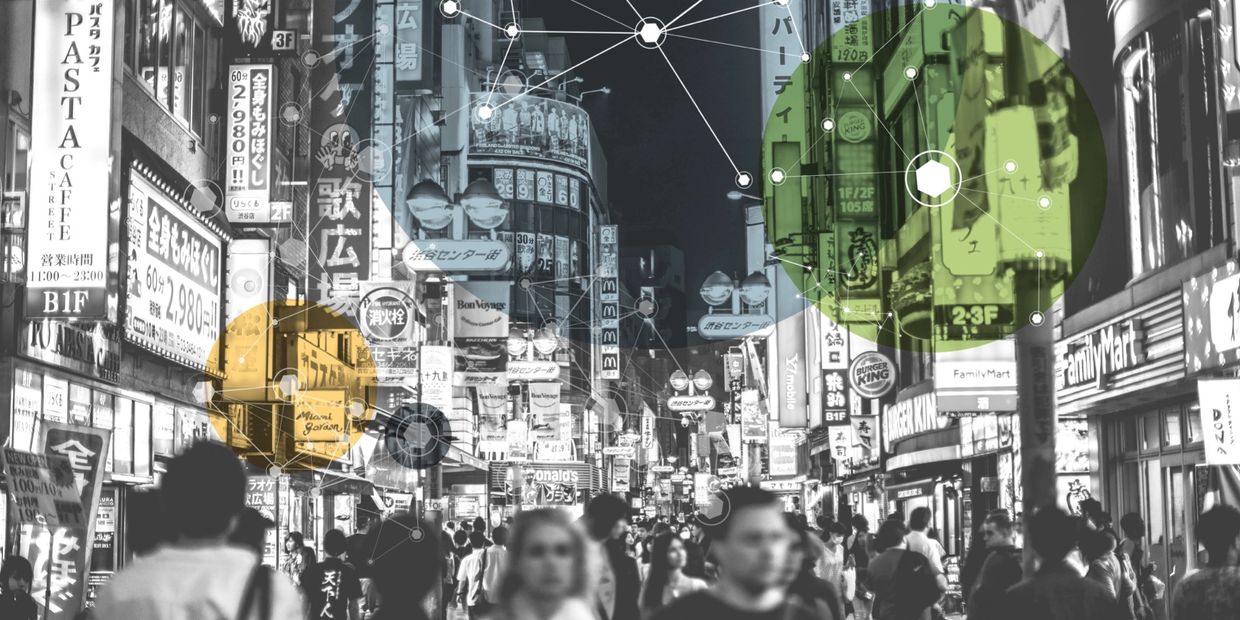
Today’s Cyber threats target people and their roles in organizations and governments rather than computer systems and networks. While attackers target victims using a variety of vectors, they rely on human error to penetrate systems of value for espionage and large financial payoffs. Inspired by the challenges of a society protecting itself against modern adversaries, our projects focus on the exploitation of social norms, values and behavior against enemies with new digital attack surfaces.
While cyber attack surfaces are still vastly unknown by most of us, their clandestine nature intrigues us. It's time for cyber security to become personal.
In response to sophisticated cyber threats, the US has aggressively modernized. Defeating the enemy requires an entirely new approach where risky alliances are formed with private companies, eccentric individuals and foreign governments. Some of these alliances involve individuals with financial and political motivations resulting in adversarial impacts. Meanwhile, cyber enemies develop highly sophisticated attack techniques, often involving individuals at targeted municipalities and NGO’s such as research institutions or utilities. The enemy uses clandestine social engineering approaches in addition to cyber skills to achieve their goals. Countermeasures and cyber threat hunting may become our only hope of restoring financial and personal safety in this new and complex existence. – The Digital Adversary
In a digital underworld of organized crime and nation state adversaries seeking political and economic influence, a team of bold, young cyber forensic agents engage in constant global battles where their personal and professional lives hang in the balance.
Official FBI Authorization Rights

FBI Right to Use
Exigent Media has official rights authorization to use the FBI seal, name, and initials as set decorations/wardrobe and on prop letterheads, ID badges, signs, etc., within cyber media series in perpetuity, domestically and internationally. This permission extends to any advertisement or promotion of the film in which the use relates to the content of the film.
Copyright © 2022 EXIGENT MEDIA LLC. - All Rights Reserved.